The Sandbox Mandate: An IT Manager’s Guide to Secure AI Agent Integration.
A guide for IT managers to securing corporate networks using sandboxes, machine identities, and Zero Trust architectures for safe agentic integration.
Brewed for Work | Issue #3, Feb ‘26 | Premium
Welcome to Brewed for Work, your Tuesday ritual for sharper thinking about careers, workplaces, and the shifting nature of professional life.
If you’re reading this as a free subscriber, consider upgrading to the paid tier for full access to deep-dive essays, exclusive workbooks, and interactive polls. Your subscription keeps this independent newsletter fully brewed and your career better caffeinated.
» » » Check out subscribers’ benefits.
In this issue of Brewed for Work, we move beyond chatbots to the real architectural hurdle: Agentic Integration.
As AI shifts from "answering" to "acting," IT and Operations Managers must secure the perimeter. We explore building "Sandboxes" using machine identities and zero-trust frameworks. Inside, discover a technical guide to isolation, a deep dive into AgentOps, and a 10-point deployment checklist.
Scale autonomy without compromising your network’s integrity. It’s time to build the walled garden.
Takeaway Resource: The Enterprise AI Sandbox Deployment Checklist
The enterprise AI landscape is shifting from passive retrieval to active execution. We are moving beyond chatbots that simply “answer” to AI Agents that “act”: querying databases, triggering API calls, and modifying files across internal systems.
For IT and Operations Managers, this transition represents a double-edged sword: the potential for unprecedented operational efficiency versus the prospect of “Shadow AI” running unchecked within the corporate perimeter.
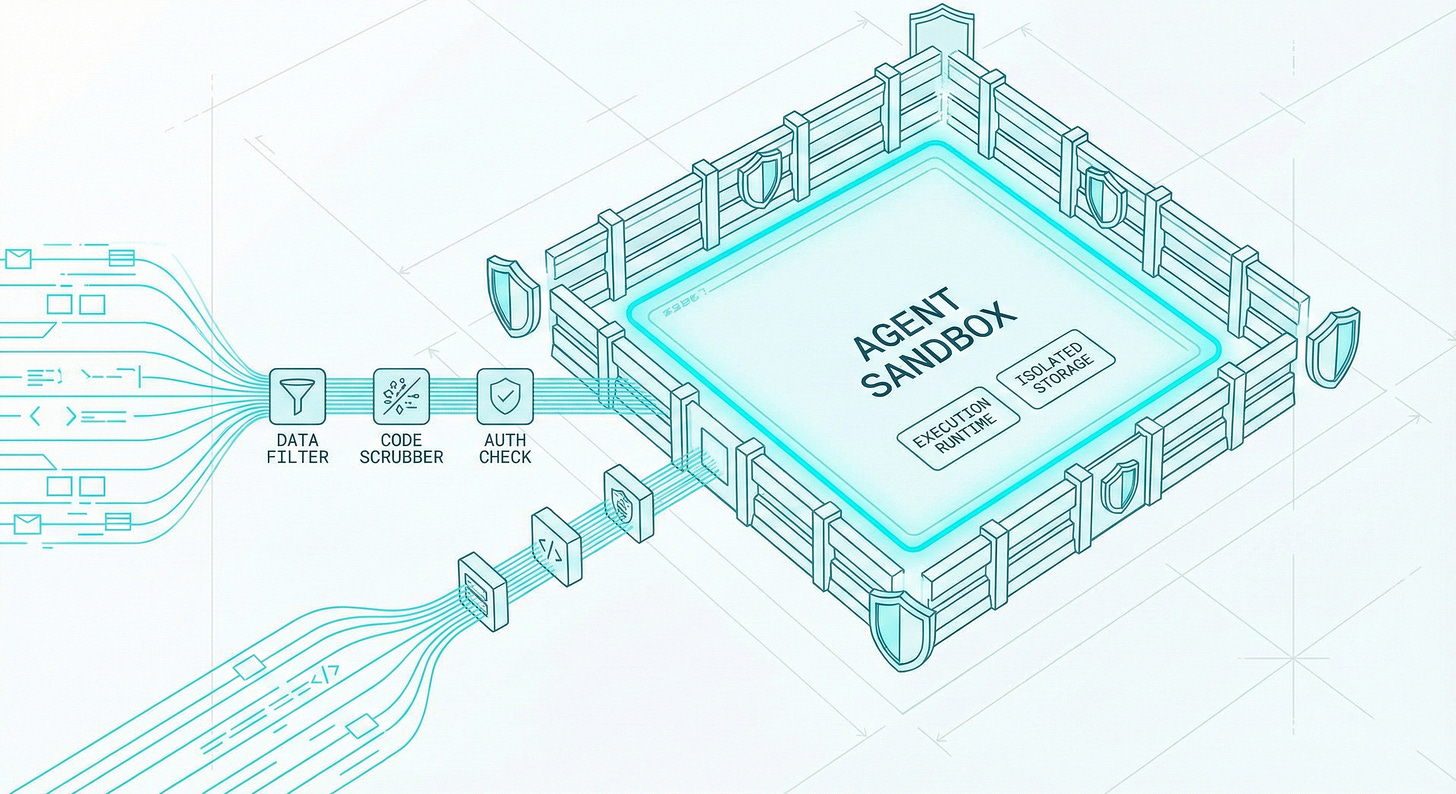
The core challenge is that traditional security protocols were designed for human users or static service accounts, not for non-deterministic agents capable of iterative reasoning. If an agent is granted broad access to a secure network, a single “prompt injection” or logic loop could result in catastrophic data exfiltration or system corruption. This post explores the architectural imperative of the “Agent Sandbox”—a containerized, least-privilege environment designed to isolate agent execution from core infrastructure.
By treating AI agents as Machine Identities rather than user extensions, enterprises can implement a “Zero Trust” framework for autonomy. We will break down the four pillars of a secure integration: Network Segmentation to prevent lateral movement, Machine-Scale IAM to enforce granular permissions, Egress Filtering to control external data flow, and Continuous Observability to audit every “thought” an agent has before it becomes an action.
The objective here is to provide “Sandbox-as-a-Service”, a secure playground where Ops teams can deploy agents that interact with production-grade data without risking the integrity of the sovereign network. In the age of agentic workflows, the sandbox is no longer just for testing; it is the foundation of the modern enterprise AI stack.